
Texas ranks among the top states for cybercrime losses, with small businesses across Central Texas facing more targeted attacks each year. For business owners in Georgetown, Round Rock, and the greater Austin metro, the question is no longer whether a cyberattack will happen. It is when. This guide breaks down the specific threats facing small businesses in our region, provides a hands-on security checklist you can implement this week, and covers the compliance basics that keep your operations protected.
Key Takeaways
- Central Texas small businesses face growing cybersecurity threats, with ransomware, phishing, and business email compromise among the most common attack types targeting companies with 10 to 75 employees.
- Industry-specific risks vary significantly. Construction firms, law offices, and manufacturers each face unique vulnerabilities that demand tailored security strategies.
- A layered defense combining employee training, endpoint protection, network security, and a tested backup and recovery plan is the most reliable way to protect your business.
- Compliance requirements like PCI-DSS and CMMC apply to many Georgetown-area businesses, and even your clients may require you to meet these standards.
- A documented incident response plan can reduce recovery time from weeks to hours and potentially save your business from permanent closure.
Why Cybersecurity Matters for Georgetown and Central Texas Small Businesses
The FBI’s Internet Crime Complaint Center reported that Texas consistently ranks in the top three states for cybercrime losses. Small businesses with fewer than 100 employees account for a significant portion of these incidents. Central Texas, with its booming economy and growing small business community, has become an increasingly attractive target.
Georgetown’s rapid growth as a business hub in Williamson County means more companies are going digital, often without the security infrastructure to match. Many businesses in the area rely on cloud-based tools, remote work setups, and digital payment systems that create new entry points for attackers.
The financial impact is severe. The average data breach costs a small business between $120,000 and $1.24 million, depending on the scope. Beyond direct financial losses, businesses face reputational damage, client trust erosion, and potential legal liability. For a 20 to 50 employee company in Georgetown or Round Rock, a single ransomware incident can mean weeks of downtime that many businesses cannot survive.
Attackers specifically target businesses they perceive as having weaker defenses. Small and mid-sized businesses in growing markets like Central Texas often lack dedicated IT security staff, making them prime targets compared to larger enterprises.
The Top Cyber Threats Targeting Small Businesses in Our Region
Phishing and Business Email Compromise
Phishing remains the number one attack vector for small businesses. Business email compromise (BEC) targets specific employees, often those in accounting or leadership roles, to authorize fraudulent wire transfers or share sensitive data. A construction company might receive an email that appears to come from a subcontractor requesting a change in payment routing. A law firm could get a message that looks like a client asking for confidential case files.
Ransomware
Ransomware encrypts your files and demands payment for their release. Small businesses are disproportionately affected because they often lack robust data backup and recovery systems. The average ransom demand now exceeds $100,000, but the real cost goes beyond the ransom. Downtime, lost productivity, and regulatory fines can multiply the total impact several times over.
Insider Threats and Human Error
Employee mistakes, such as clicking a malicious link, using weak passwords, or misconfiguring cloud storage, cause a substantial portion of security incidents. For businesses in Georgetown and Round Rock that rely on a mix of in-office and remote workers, managing access controls across all work environments is especially challenging.
Supply Chain Attacks
Central Texas small businesses often work within larger project ecosystems, particularly in construction, manufacturing, and engineering. A compromised vendor or partner can serve as a backdoor into your network through trusted communication channels. When your software vendors push a compromised update or a partner’s email system gets breached, attackers gain access through the trust relationships you have already established. Vetting your vendors’ security practices and limiting third-party access to only what is necessary are essential defensive steps.
Schedule a 15-Minute Call to get a confidential assessment of your current cybersecurity risks.
Industry-Specific Cybersecurity Risks
Construction and Engineering
Construction companies handle large financial transactions, complex project bids, and detailed blueprints with real value to attackers. Key risks include wire fraud through BEC during the draw process, blueprint and bid theft, unsecured job site devices connecting to open networks, and multiple subcontractors accessing shared project management platforms. Firms in the Georgetown and Round Rock area should ensure that all financial transactions require multi-step verification and that project platforms use role-based access controls.
Legal Services
Law firms hold privileged communications, financial records, and confidential case strategy. Texas attorneys have professional obligations to safeguard client information, and a breach can trigger bar disciplinary action. Attorneys accessing case files from home or court locations often use personal devices or public Wi-Fi, creating additional exposure. For Georgetown-area law offices, implementing encrypted file sharing and mandatory VPN connections for remote access are baseline requirements that protect both the firm and its clients.
Manufacturing
Manufacturers in Central Texas increasingly rely on connected operational technology systems, industrial IoT sensors, and cloud-based supply chain tools. Hackers can disrupt production lines by targeting industrial control systems, steal proprietary designs, or exploit supply chain relationships. Manufacturers working with Department of Defense contracts must also meet CMMC standards.
The Georgetown Small Business Cybersecurity Checklist
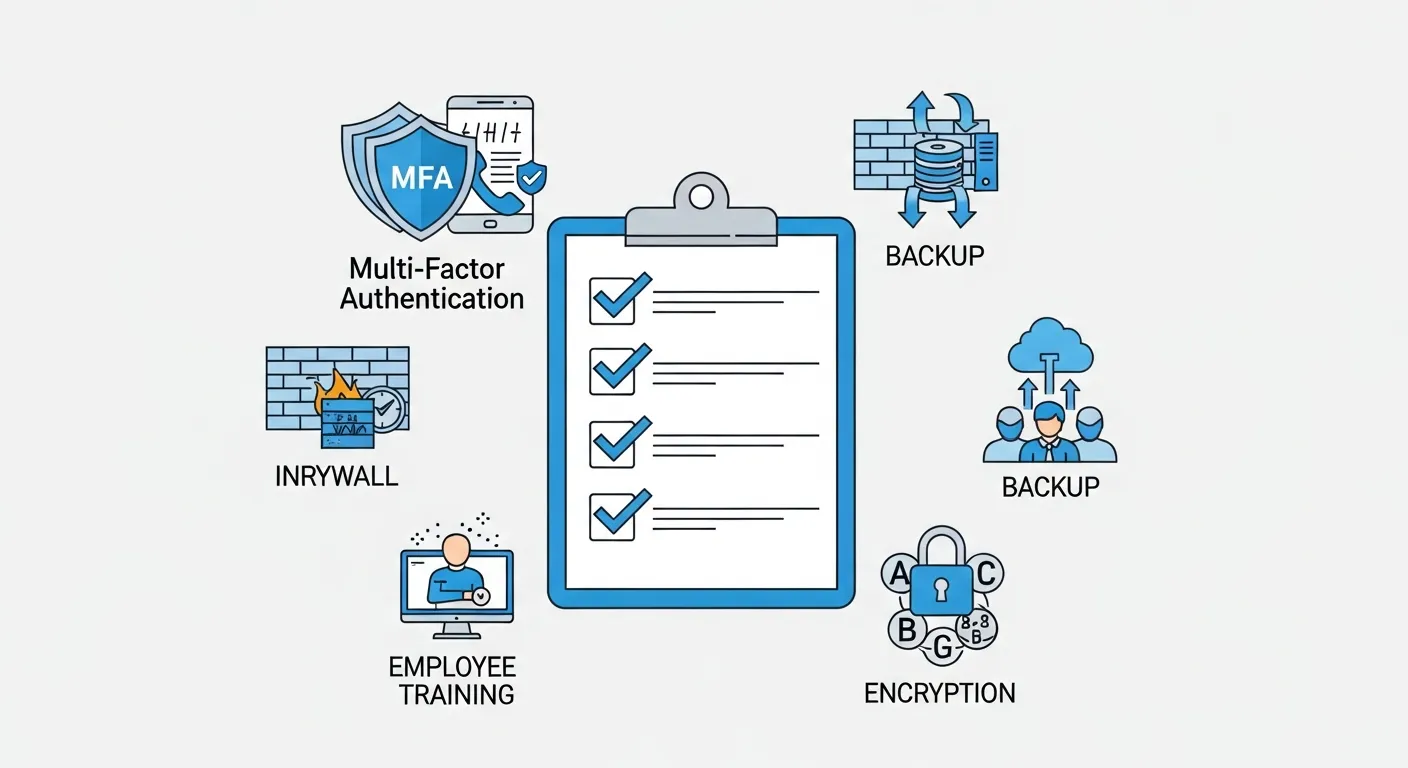
Use this checklist to evaluate your current security posture. Each item is actionable and can be implemented without a massive budget.
Access and Authentication
- Enable multi-factor authentication (MFA) on all business email, cloud platforms, and financial systems
- Implement a password policy requiring unique passwords of at least 14 characters
- Deploy a business-grade password manager for all employees
- Review and revoke access for former employees and unused accounts quarterly
- Use role-based access controls so employees only access what their job requires
Endpoint and Network Security
- Install business-grade endpoint protection on all devices
- Keep all operating systems and software updated with the latest security patches
- Configure your firewall to block unauthorized traffic
- Segment your network so guest Wi-Fi, IoT devices, and critical systems are isolated
- Use a VPN for all remote access connections
Email and Data Protection
- Configure email filtering to block malicious senders and suspicious attachments
- Enable DMARC, DKIM, and SPF records on your email domain
- Train employees to verify payment or data requests through a second channel
- Maintain at least three copies of critical data on two different storage types, with one copy offsite
- Test backup restoration at least quarterly
Employee Training
- Conduct cybersecurity awareness training at least twice per year
- Run simulated phishing tests quarterly
- Establish a no-blame reporting process for suspected security incidents
- Include cybersecurity responsibilities in onboarding for every new hire
Compliance Basics for Central Texas Businesses
PCI-DSS
If your business accepts credit card payments, PCI-DSS compliance is mandatory. Key requirements include encrypting cardholder data, maintaining secure networks, and regularly testing security systems.
CMMC
Manufacturers and contractors working with the Department of Defense must achieve CMMC certification. Prime contractors in Central Texas may require subcontractors to meet specific CMMC levels even for indirect work.
Texas Data Breach Notification Law
Texas requires businesses to notify affected individuals within 60 days of discovering a data breach involving sensitive personal information. If more than 250 residents are affected, you must also notify the Texas Attorney General.
Following established security frameworks demonstrates due diligence to your clients and partners. Many Georgetown-area businesses find that aligning with a recognized framework helps them win contracts with larger organizations that require vendor security assessments through IT consulting engagements.
Building Your Incident Response Plan
A documented incident response plan is the single most important thing you can do to limit the damage of a cyberattack.
Preparation: Designate an incident response team (even if it is just two or three people), document your critical systems and recovery priorities, and establish relationships with your managed IT provider, legal counsel, and cyber insurance carrier. Store your plan both digitally and in printed form, since your digital systems may be compromised during an incident.
Detection and Containment: Monitor for unusual activity like unexpected login attempts or large data transfers. When an incident is confirmed, isolate affected systems immediately and disable compromised accounts. Preserve evidence for investigation.
Recovery: Remove the threat, restore data from clean backups after verifying they are not compromised, and patch the vulnerability that allowed the incident. Monitor systems closely for signs of reinfection.
Post-Incident Review: Conduct a review within one week. Document lessons learned, update your security measures, revise your incident response plan, and notify affected parties as required by Texas law.
Compliance Requirements for Central Texas Businesses
Beyond general cybersecurity best practices, many Georgetown and Central Texas businesses must meet specific regulatory and contractual compliance requirements. Understanding which standards apply to your business is essential for avoiding fines, legal liability, and the loss of client trust.
Texas Data Breach Notification Law
Texas Business and Commerce Code Chapter 521 requires any business that owns or licenses computerized personal information to notify affected individuals within 60 days of discovering a breach. If more than 250 Texas residents are affected, you must also notify the Texas Attorney General. Personal information includes names combined with Social Security numbers, driver license numbers, financial account numbers, or health information. Failing to comply can result in civil penalties of up to $250,000 per violation. For a Georgetown business with even a modest customer database, a single unnotified breach could trigger significant legal exposure.
PCI-DSS for Payment Processing
Any business that accepts credit card payments, whether through a point-of-sale terminal, online portal, or over the phone, must comply with the Payment Card Industry Data Security Standard. This applies to retail shops in Georgetown, professional services firms in Round Rock, and construction companies processing draw payments. Key requirements include encrypting cardholder data, maintaining a firewall, restricting access on a need-to-know basis, and conducting regular vulnerability scans. Non-compliance can result in fines from payment processors and personal liability in the event of a breach.
CMMC for Defense Contractors
Central Texas manufacturers and engineering firms working with Department of Defense contracts must meet the Cybersecurity Maturity Model Certification. Even subcontractors handling Controlled Unclassified Information must achieve at least CMMC Level 2, which requires 110 security controls aligned with NIST SP 800-171. For a manufacturing company in Williamson County, this means documenting access controls, encrypting data at rest and in transit, implementing incident response procedures, and passing a third-party assessment. The timeline for enforcement has accelerated, and contracts now increasingly require CMMC certification as a prerequisite.
HIPAA for Healthcare-Adjacent Businesses
If your business provides services to healthcare organizations, such as IT consulting, accounting, or legal support for medical practices, you may qualify as a Business Associate under HIPAA. This means you must implement administrative, physical, and technical safeguards for any protected health information you access. Georgetown-area businesses serving healthcare clients should ensure they have a signed Business Associate Agreement and maintain HIPAA-compliant data handling practices, including encrypted storage, access logging, and workforce training.
Contractual Compliance
Even without regulatory mandates, your clients may require cybersecurity standards as a condition of doing business. Construction general contractors increasingly require subcontractors to demonstrate specific security controls. Real estate firms require secure document handling. Accounting firms need to show they protect client financial data. Meeting these contractual requirements protects your revenue streams and competitive position in the Georgetown business community.
IT consulting from a local provider who understands these compliance requirements can help you build a roadmap that satisfies your regulatory obligations without overcomplicating your operations.
Practical Tips That Work on Any Budget
You do not need an enterprise budget to meaningfully improve your security posture. Here are cyber security best practices that deliver the highest return on investment for small businesses.
Multi-factor authentication alone stops over 99% of automated account compromise attacks. If you implement nothing else from this guide, turn on MFA for every business account today. It is free with most cloud services and takes minutes to configure. Combine this with automatic security updates and automated backup schedules to reduce your dependence on human vigilance.
Employee training has the highest return on investment of any security measure. A single phishing awareness session can reduce click-through rates on malicious emails by over 60%.
A cybersecurity risk assessment identifies gaps you may not see from the inside. Working with a local IT provider who understands the regional threat landscape and your industry is more effective than a generic approach.
Schedule a 15-Minute Call with Computek to get a free, confidential cybersecurity risk assessment for your business.
Related: Want the full picture? Read our comprehensive guide to IT services in Georgetown.
Frequently Asked Questions
What is the biggest cybersecurity threat to small businesses?
Phishing and business email compromise are the most common and damaging threats. These attacks exploit human trust rather than technical vulnerabilities, which is why employee training is just as important as technical controls.
How often should we test our backups?
Test a full backup restoration at least quarterly. Businesses with higher data volumes or stricter compliance requirements should test monthly. A backup that has never been tested is a backup you cannot trust.
Does my business need cyber insurance?
Cyber insurance is increasingly important for small businesses handling sensitive data or processing payments. It can cover incident response costs, legal fees, notification expenses, and business interruption losses.
What should I do if I think my business has been hacked?
Immediately isolate affected systems from your network, document what you observe, and contact your IT provider. Do not attempt to negotiate with attackers or pay ransoms without professional guidance. Having a pre-established relationship with a managed IT provider means expert help within hours rather than days.
How can small businesses improve their cybersecurity posture?
Start with the checklist in this guide. Enable MFA everywhere, train your employees, implement a tested backup strategy, and get a professional security assessment. A managed IT services partner can handle the technical complexity while you focus on running your business.
Protect Your Georgetown Business Today
Cybersecurity for small businesses is not a luxury. It is a fundamental requirement for operating in today’s digital environment. The businesses in Georgetown, Round Rock, Cedar Park, and across Central Texas that take proactive steps today will be the ones still thriving when less-prepared competitors are recovering from preventable attacks.
Computek has been protecting Central Texas businesses for over 25 years. As Georgetown’s longest-tenured IT services provider, we understand the specific challenges that local businesses face, from construction firms managing multi-million-dollar projects to law offices safeguarding privileged communications.
Start with the checklist in this guide. Identify your gaps. Then take the next step.
Schedule a 15-Minute Call with Computek to get a free, confidential cybersecurity risk assessment for your business.
